Eliminate Cyber Trap VST Crack 2024 Free Download
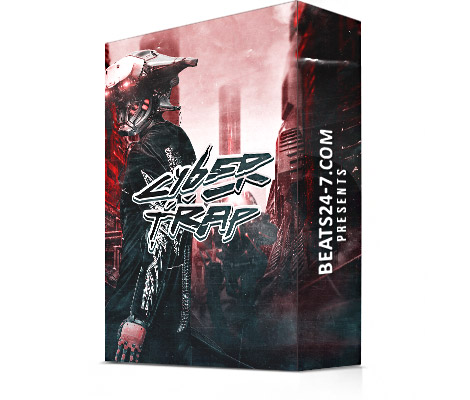
Eliminate Cyber Trap VST Crack is one of the best bass packages with high-quality and professional sounds. The program lets users add the included content to their projects and mix it with other sounds to make unique and rich soundtracks. This is done seamlessly. The bundle gives users access to more than 880 samples to help them be more creative and productive when making their music. Also, this audio content makes it easy for customers to show off their creativity without breaking their concentration and starting from scratch.
In an era dominated by technology, the threat landscape of the digital world has expanded, giving rise to the need for robust cybersecurity measures.
This article explores strategies to eliminate the cyber trap, empowering individuals and organizations to navigate the digital maze safely and securely.
1. User Education and Awareness:
- The first line of defense against cyber threats is informed users.
- Educating individuals about common cyber risks, phishing tactics, and the importance of strong passwords cultivates a vigilant digital culture.
- Awareness programs empower users to recognize and resist potential traps, reducing the likelihood of falling victim to cyber-attacks.
2. Multi-Factor Authentication (MFA):
- Implementing Multi-Factor Authentication adds an extra layer of security by requiring users to provide multiple forms of identification before gaining access.
- This simple yet effective measure significantly reduces the risk of unauthorized access, creating a formidable barrier against cyber traps.
3. Regular Software Updates:
- Cyber attackers often exploit vulnerabilities in outdated software.
- Regularly updating operating systems, antivirus programs, and other software ensures that security patches are applied promptly, minimizing the potential entry points for cyber traps.
4. Secure Password Practices:
- The strength of passwords is paramount in preventing unauthorized access.
- Encouraging the use of complex, unique passwords and regular password updates fortifies digital defenses.
- Password manager tools can also enhance security by generating and storing strong, encrypted passwords.
5. Endpoint Protection:
- Deploying robust endpoint protection solutions shields devices such as computers, laptops, and smartphones from malicious software.
- Antivirus programs and endpoint security tools act as guardians against cyber traps, actively scanning and neutralizing potential threats.
6. Network Security Measures:
- Securing network infrastructure is critical to preventing cyber traps.
- Implementing firewalls, intrusion detection and prevention systems, and secure Wi-Fi protocols safeguards against unauthorized access and data breaches, creating a resilient digital perimeter.
7. Incident Response Planning:
- No system is completely immune to cyber threats.
- Developing an incident response plan enables swift and effective action in the event of a security breach.
- Timely identification, containment, eradication, and recovery are essential components of a comprehensive response strategy.
8. Collaboration with Cybersecurity Professionals:
- Engaging with cybersecurity experts ensures a proactive and adaptive approach to digital security.
- Collaborating with professionals who specialize in threat intelligence, penetration testing, and security audits provides organizations with valuable insights to continually enhance their cybersecurity posture.
Key Features:
- Simple and easy to use.
- It can be mixed to make professional soundtracks.
- Content that sounds unique and full.
- There were more than 130 loops and 625 one-shots.
- Integration that is fast and easy.
- Immediate access to all content.
System Requirements:
- Hard Disk Space: 550 MB of free space required.
- Operating System: Windows 7/8/8.1/10.
- Memory (RAM): 512 MB of RAM is required.
- Processor: Intel Dual Core processor or later.
How To Install Eliminate Cyber Trap VST Crack?
- Firstly, Get the download link given below.
- Secondly, Extract the file from the downloaded folder.
- Thirdly, Install the program in the normal way.
- Then, follow the instructions given in the text.
- That’s All, Enjoy Now!
- Thanks For Visiting!
Download Link is Given Below…
